Information Security Policy
LIST OF ACRONYMS
BIM: Building Information Modeling
ENS: National Security Scheme
LOPDGDD: Personal Data Protection and Digital Rights Guarantee Act
POC: Person of Contact
RRHH: Human Resources
SGI: Integrated Management System
SGSI: Information Security Management System
SI: Information Security
TIC: Information and Communication Technologies
1. PURPOSE AND SCOPE
The Executive Management of INGECID S.L. (hereinafter INGECID), within the framework of its general and non-delegable competence to determine the general policies and strategies of the organization, approves this policy.
The purpose of this policy is to define and establish the principles, criteria and improvement objectives governing actions in matters of Information Security (SI) of INGECID’s systems that are subject to the Information Security Management System (SGSI) and within the scope of Royal Decree 311/2022, of May 3, regulating the National Security Scheme (ENS) [1].
This policy applies to all INGECID information systems, to the persons comprising its organization and to its service providers or Information and Communication Technology (TIC) solution providers.
Therefore, this policy is limited to INGECID’s services and systems, included within the scope of the SGSI, and that provide coverage for compliance with the security requirements and measures established in the ENS [1], that is, to the information systems that support the services of:
- Design and development of civil engineering projects and technical reports.
- Training for companies in areas of knowledge of civil engineering and building construction.
- Engineering in the field of nuclear energy.
- Software development for the fields of civil engineering and nuclear energy.
2. ACTIVITIES
2.1 Mission and Objectives
INGECID’s mission is contained in document SGI-04 Mission, Purpose and Strategy [2], published on the organization’s website (www.ingecid.es).
Furthermore, the security objectives that INGECID intends to guarantee with this policy are:
- Ensure the confidentiality, integrity, authenticity of information and continuity in the provision of services.
- Implement security measures that enable traceability of access and respect, among others, the principle of least privilege, also reinforcing the duty of confidentiality of users regarding the information they access in the performance of their duties.
- Implement security measures based on risk.
- Train and raise awareness among INGECID members regarding information security.
- Deploy and control physical security by ensuring that information assets are located in secure areas, protected by access controls, attending to detected risks.
- Establish security in communications management through necessary procedures, ensuring that information transmitted through communications networks is adequately protected.
- Control the acquisition, development and maintenance of information systems throughout all phases of the information systems lifecycle, ensuring security by default.
- Control compliance with security measures in the provision of services, maintaining control over the acquisition and incorporation of new system components.
- Manage security incidents for the correct detection, containment, mitigation and resolution thereof, adopting necessary measures to prevent their recurrence.
- Protect personal data, adopting technical and organizational measures in response to risks arising from processing in accordance with data protection legislation.
- Continuously supervise the security management system, improving and correcting detected inefficiencies
2.2 Principles
This security policy is established in accordance with the basic security principles set out in Article 5 of the ENS [1], that is:
- Security as an integral process
- Risk-based security management
- Prevention, detection, response and preservation
- Existence of lines of defense
- Continuous monitoring
- Periodic reevaluation
- Differentiation of responsibilities
In accordance with the provisions of Article 12 of the ENS [1] and in proportion to the risks identified in each system, these principles are developed by applying the following minimum requirements:
- Organization and implementation of the security process
- Risk analysis and management
- Personnel management
- Professionalism
- Authorization and control of access
- Protection of facilities
- Acquisition of security products and contracting of security services
- Least privilege
- System integrity and updating
- Protection of stored and in-transit information
- Prevention regarding other interconnected information systems
- Activity logging and malicious code detection
- Security incidents
- Business continuity
- Continuous improvement of the security process
2.3 Regulatory Framework
The main legislation affecting this policy is Royal Decree 311/2022, of May 3, regulating the National Security Scheme (ENS) [1].
Furthermore, within process PC-ES-02 Context Analysis [3], INGECID carries out systematic registration of identification and evaluation of legal requirements and other applicable requirements. This registration allows identifying, analyzing and verifying the degree of adequacy and compliance with all current legislation, among others, in matters of information security affecting the organization.
Finally, contractual requirements derived from agreements with clients and suppliers are also expressly considered, especially those imposing specific requirements regarding information security and privacy, ensuring their integration into the company’s SGSI.
2.4 Security Organization
2.4.1 SGSI Organization Chart
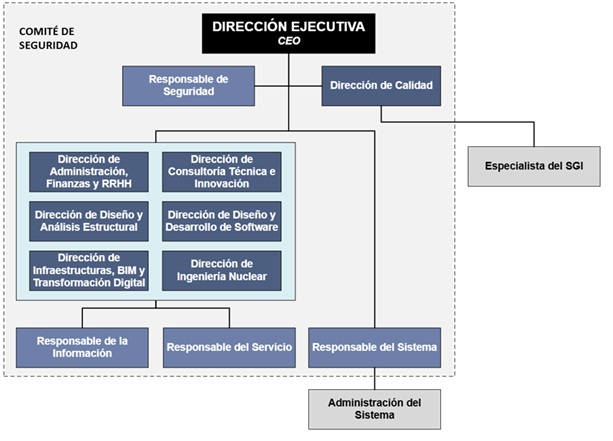
Figure 1: SGSI Organization Chart
2.4.2 Coordination Mechanisms
The security organization in INGECID is structured through the Information Security Committee, constituted by:
- Executive Management
- Department Directors:
- Administration, Finance and RRHH
- Quality
- Technical Consulting and Innovation
- Structural Design and Analysis
- Software Design and Development
- Infrastructure, BIM and Digital Transformation
- Nuclear Engineering
- Information Officer
- Security Officer
- Service Manager
- System Manager
The person responsible for Security is designated as the Person of Contact (POC) of the organization in security matters.
The roles cited above are designated by the Executive Management and their renewal must have the approval of the Information Security Committee.
Within the execution of process PC-AP-08 Human Resources [4], the functions and responsibilities are defined, both of the Information Security Committee and of each of the security roles that constitute it.
The periodicity of meetings of this committee shall be at least semi-annually, and may meet as many times as its members deem appropriate. Furthermore, taking into account the topics to be discussed, any persons that the members of this committee decide may attend the meetings.
The roles and responsibilities regarding the SGSI are communicated to new hires and periodically reminded to all organization personnel.
2.4.3 Functions and Responsibilities
2.4.3.1 Information Security Committee
- Communicate and comply with this policy and associated procedures.
- Define the organizational context and possible changes therein.
- Identify the needs and expectations of our interested parties in matters of information security, as well as their relevant requirements.
- Promote thinking in terms of risk and the action plan to reduce risk, being a proactive team.
- Approve the information security risk analysis and approve the acceptance of the residual risk level.
- Determine the criteria and methods necessary to ensure that both the operation and control of processes are effective.
- Detect areas for improvement or establish improvement plans when necessary, identifying changes or inclusion of new techniques, products, procedures or documentation in general that may improve the performance and effectiveness of the management system.
- Review documented information and contribute to its improvement.
- Analyze newly detected threats.
- Ensure that objectives, including those necessary to meet service requirements, are established at the relevant functions and levels.
- Detect needs for awareness and training actions.
- Transmit complaints, claims or suggestions, as well as collaborate in the resolution of incidents, non-conformities and corrective actions.
- Schedule and participate in audits.
- Collaborate to carry out management reviews.
- Plan new Business Continuity Plan drills.
- Assess damages and determine the need for disaster declaration and activation of the Recovery Plan.
2.4.3.2 SGSI Roles
The functions and responsibilities of the Security Officer, System Manager, Information Officer and Service Manager roles are duly recorded in their corresponding role sheet. These sheets are defined and approved by the Executive Management within the framework of process PC-AP-08 Human Resources [4], which also records the appointment (assignment of roles) to the corresponding persons.
2.4.4 Conflict Resolution
In case of conflict between the different managers comprising the organizational structure of this policy, it shall be resolved by the Executive Management, and the greater requirements derived from the protection of personal data shall prevail.
2.5 System Security Documentation
The documented information related to compliance with the ENS [1] is organized, coded and approved in accordance with the general requirements established in INGECID’s management system, within the framework of process PC-AP-09 Knowledge Management [5].
All documentation linked to the different management systems, including specifically that related to the ENS [1], is centralized and stored in INGECID’s corporate information systems, ensuring its accessibility, integrity, traceability and version control.
2.6 Compliance Obligations
2.6.1 Personnel
All INGECID personnel have the obligation to know and comply with this Security Policy and the procedures, instructions and other documented information of the SGI that develops it, being INGECID’s responsibility, through the Security Committee, to provide the necessary means for the information to reach those affected.
2.6.2 Third Parties
2.6.2.1 CLIENTS
When INGECID provides services to other entities or handles their information, they shall be made aware of this policy, without prejudice to respecting data protection regulations if acting as data processor in the provision of said services, and channels shall be established for reporting and coordination of the respective Security Committees and procedures for reaction to security incidents.
2.6.2.2 COLLABORATORS AND SUPPLIERS
When INGECID uses third-party services or discloses information to third parties, they shall be made aware of this policy and the security rules, procedures and/or instructions pertaining to said services or information, without prejudice to compliance with other obligations regarding data protection. This third party shall be subject to the obligations established in said documentation, being able to develop their own operational procedures to satisfy it. Specific procedures for reporting and resolving incidents are established. It shall be ensured that third-party personnel are adequately aware of security matters, at least at the same level as established in this policy.
When any aspect of the policy cannot be satisfied by a third party as required in the preceding paragraphs, the person responsible for Security shall issue a report specifying the risks incurred and the manner of treating them. Approval of this report by the persons responsible for the affected information and services shall be required before the start of contracting.
These obligations shall be regulated by agreement, convention or contract defining the relationship with third parties.
2.7 Awareness and Training
Within the framework of process PC-AP-08 Human Resources [4], training and awareness actions are developed aimed at all personnel, with the objective of promoting an organizational culture oriented towards information security. These actions shall include, among others, the following contents:
- Information Security Policy.
- Fundamentals of information security and its application in the work environment.
- Identification and management of risks, vulnerabilities and threats in information systems.
- Importance of compliance with current legislation regarding security and data protection.
All INGECID personnel must attend, at least once a year, an information security training session. Furthermore, continuous awareness actions shall be established, with special attention to new hires, who shall receive specific training during their onboarding process.
Persons performing functions related to the use, operation or administration of TIC systems shall receive specialized training to ensure safe handling of systems, according to their position requirements. This training shall be mandatory before assuming any responsibility, whether due to new hire, position change or function reassignment.
2.8 Risk Management
All information systems affected by this policy, as well as all personal data processing carried out by INGECID, must be subject to a risk analysis that allows identifying, evaluating and managing the threats and risks to which they are exposed.
This analysis shall be carried out in the following cases:
- Periodically, at least once a year.
- When significant changes occur in the managed information or in the services provided.
- Following the occurrence of a serious security incident or the detection of critical vulnerabilities that may compromise the confidentiality, integrity, availability, authenticity and traceability of information.
The Security Officer shall be responsible for ensuring the performance of the risk analysis, as well as identifying deficiencies and weaknesses in systems and processes. Likewise, they must inform the Security Committee of the results obtained and propose necessary corrective or improvement measures.
2.9 Personal Data
INGECID shall only collect personal data when these are adequate, relevant and strictly necessary in relation to the legitimate purposes for which they have been obtained. At all times, technical and organizational measures necessary to ensure compliance with current personal data protection legislation shall be adopted.
When an INGECID information system manages personal data, the provisions of the Personal Data Protection and Digital Rights Guarantee Act (LOPDGDD) [6], as well as its implementing rules, shall apply. All this without prejudice to the additional compliance with the requirements established in the ENS [1].
Likewise, all information systems must adjust to the security levels required by data protection regulations, depending on the nature, scope, context and purposes of the processing, as well as the risks identified for the rights and freedoms of persons.
2.10 Review and Approval
In order to guarantee the validity, adequacy and effectiveness of this document, two types of review activities are established:
- Systematic periodic reviews: carried out in a planned manner, at least once a year by the Information Security Committee.
- Unplanned reviews: carried out in response to:
- any security event or incident that could entail a significant increase in the current risk level or has caused an impact on INGECID’s information security
- detection of relevant incidents
- existence of changes in the legal or regulatory framework that may affect the validity of this policy.
Finally, if as a result of such reviews, it is necessary to modify this policy, the approver of the new policy shall be the Executive Management of INGECID and interested parties shall be duly informed through the same channels used for its dissemination.
3. REFERENCES
[1] Royal Decree 311/2022, of May 3, regulating the National Security Scheme (ENS).[2] INGECID, SGI-04 Mission, Purpose and Strategy.[3] INGECID, PC-ES-02 Context Analysis.[4] INGECID, PC-AP-08 Human Resources.[5] INGECID, PC-AP-09 Knowledge Management.[6] Organic Law 3/2018, of December 5, on Personal Data Protection and guarantee of digital rights (LOPDGDD).
Prepared by the Information Security Officer and approved by the Executive Management
APPROVAL DATE: October 3, 2025
DOCUMENT: SGI-03
REVISION: 00



